AI-powered Layer 7 DDoS mitigation and bot detection at the edge
Deploy Baskerville in front of your origin using Cloudflare’s edge. Inspect requests, fingerprint clients, score suspicious behaviour through Baskerville’s ML pipelines, and enforce policies using challenges, rate limiting, and blocking, all without disrupting legitimate users.
How it works
Baskerville is deployed at the edge in front of your origin, using Cloudflare to receive and proxy inbound traffic before it reaches your service. Requests are inspected in real time, enriched with metadata and fingerprints, and evaluated against customer-defined policies and detection logic. Clean traffic is forwarded upstream, while suspicious traffic can be challenged, rate limited, or blocked.
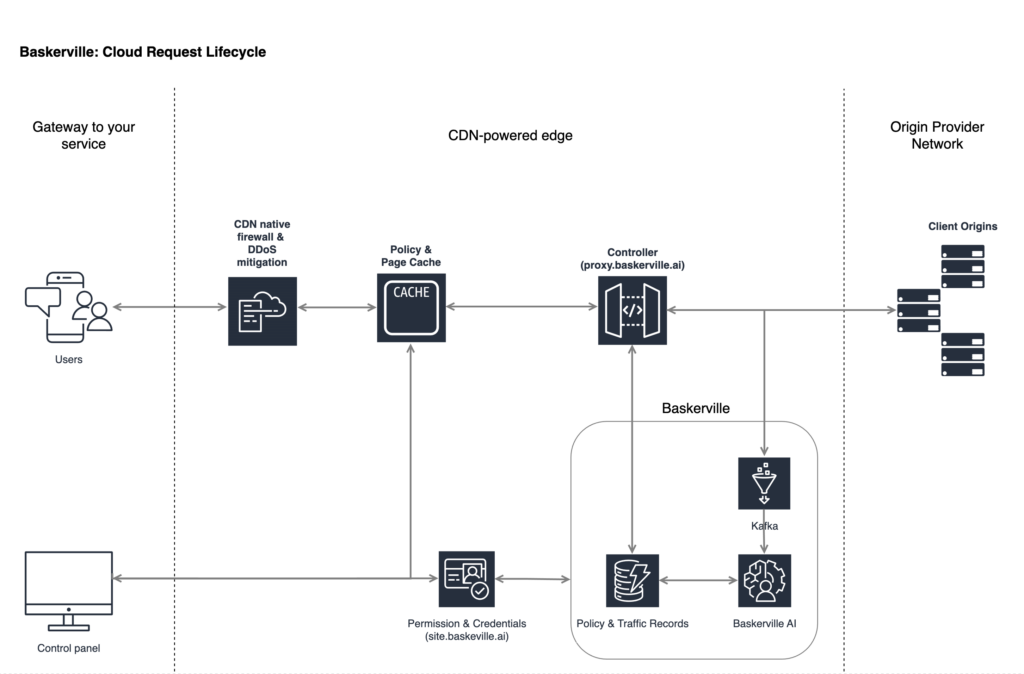
In parallel, request signals are fed into Baskerville’s analysis pipeline, where behavioural patterns can be identified across sessions, sources, and attack waves. Predictions are then pushed back into the enforcement layer so that future requests can be handled more precisely. This creates a continuous protection loop that combines edge enforcement, behavioural detection, and adaptive policy control.
Deployment model
Designed for teams already on Cloudflare, the integration offers a seamless onboarding experience. Customers can authorize Baskerville to make the required DNS changes, allowing existing A and AAAA records to be converted to CNAMEs that route traffic through the Baskerville layer with minimal operational overhead.
This model lets Baskerville enforce protections before application infrastructure is exposed, while still preserving flexible control over how traffic is handled. Suspicious requests can be challenged, rate limited, or blocked at the edge, while clean traffic continues to flow to origin with minimal disruption.
Edge enforcement
Baskerville sits in front of customer origins on Cloudflare’s edge, acting as a gateway for inbound traffic. At this layer, requests can be inspected, filtered, and proxied before they ever reach the protected service.
Behavioural analysis
Request metadata and client fingerprints are collected and analyzed to detect suspicious automation, abusive patterns, and Layer 7 attack behaviour that may not be obvious from a single request alone.
Adaptive policy feedback
Detection results are fed back into the enforcement layer so that subsequent requests can be handled with greater accuracy. Teams can also define their own rules and adjust policies through the Baskerville control plane.
Enforcement
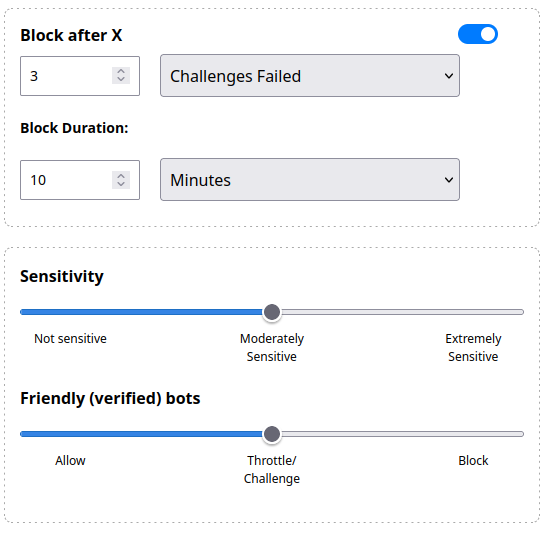
Baskerville gives operators flexible controls for responding to malicious or suspicious traffic without treating every request the same.
Built for real traffic, not just static rules
Baskerville combines WAF-style controls with fingerprinting, behavioural analysis, and machine learning feedback so enforcement can improve as attack patterns evolve.
- Block clearly malicious requests before they reach your origin
- Rate limit abusive clients and repeated high-volume request patterns
- Challenge suspicious users with CAPTCHA or Turnstile
- Allow or exempt trusted traffic, verified bots, or business-critical flows
- Apply custom policies based on request attributes, traffic patterns, or operational requirements
Control plane
Operate protection through a single control plane
Baskerville gives operators direct control over how protections are applied across their Cloudflare deployment. Through the control plane, teams can create and tune policies, review traffic patterns, monitor mitigations, and adjust enforcement without rebuilding infrastructure.
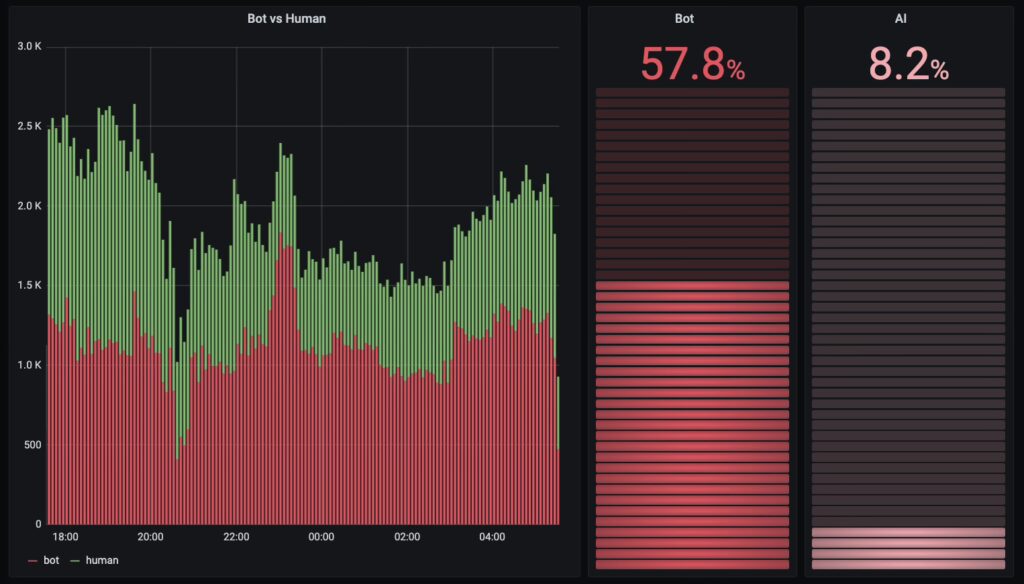
Use dashboards and analytics to understand attack activity, inspect suspicious traffic, and measure how policies are performing over time. Operators can define custom rules, review enforcement outcomes, and adapt protection posture as traffic patterns change.
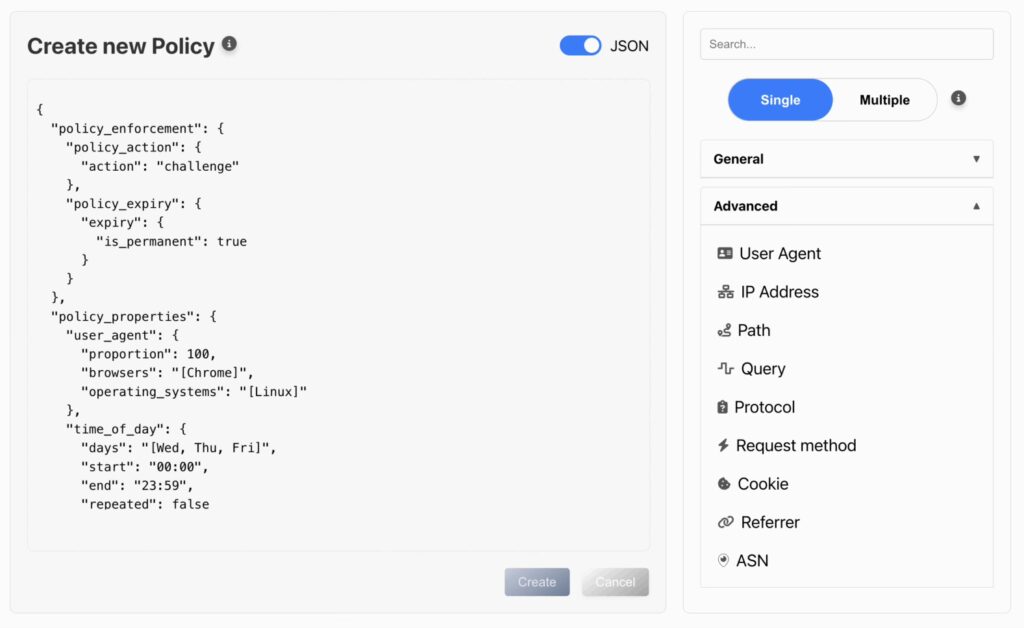
Policy management
Create and adjust policies based on request attributes, behaviour, geography, ASN, path, or operational needs.
Traffic visibility
Monitor challenged, rate-limited, and blocked traffic through dashboards, analytics, and geographic views.
Operational control
Tune enforcement, update settings, and respond quickly as attack patterns evolve.
Depend on Machine Learning protection for everything else
Instead of relying only on signatures or one-off request inspection, Baskerville continuously improves enforcement by combining traffic analysis, machine learning predictions, and operator-defined policy control. This makes it possible to respond more precisely to malicious traffic while reducing unnecessary friction for legitimate users.
Beyond static rules
Detection is informed by behaviour and traffic patterns, not just request-by-request inspection.
Adaptive enforcement
Predictions are fed back into the enforcement layer so protection can evolve as attacks change.
Operator control
Teams can define their own policies, tune enforcement, and maintain visibility through the control plane.
Built for modern application protection
Baskerville is designed for teams that need more than static edge filtering. Whether the goal is reducing origin load, controlling abusive automation, or protecting sensitive application flows, Baskerville gives teams the visibility and control needed to adapt protections as traffic changes.
Reduce unnecessary origin exposure
Inspect and enforce traffic decisions before malicious requests reach customer infrastructure.
Respond to evolving attack patterns
Use behavioural analysis and feedback-driven enforcement to detect abuse that static rules may miss.
Maintain operator control
Create policies, review traffic outcomes, and tune enforcement through a dedicated control plane.
Minimize friction for legitimate users
Apply challenges, rate limits, and blocking selectively so protection can be strong without degrading real-user access.
Use Cases
Baskerville on Cloudflare can be used to protect a wide range of customer-facing services against malicious automation, abusive behaviour, and Layer 7 attacks.
Layer 7 DDoS mitigation
Protect application endpoints from high-volume HTTP abuse before requests reach your origin.
Bot detection and management
Identify scrapers, abusive automation, and unwanted agents while allowing legitimate traffic to continue.
Application protection
Apply custom policies to sensitive paths such as login, search, checkout, APIs, or other business-critical workflows.
Adaptive mitigation for evolving attacks
Use behavioural analysis and feedback-driven enforcement to respond to attack patterns that static rules alone may miss.
See Baskerville in action
Explore how Baskerville can be deployed on Cloudflare to protect your origins from bots, abusive automation, and Layer 7 attacks while keeping legitimate traffic moving.